Hi, this is Darrell Tonneau of Solutions Reservoir and welcome to cybersecurity in the US Department of Defense. This is part three of our three-part cybersecurity tutorial. These videos follow the more comprehensive and timely material on the Solutions Reservoir website. As before, pause on slides with yellow background to review reference material. Part one was an introduction to cybersecurity and part two discussed the US government's role in the field. Part three looks at key references and focuses on the DoD and its cybersecurity alignment with other parts of the government. This is exemplified by the adoption of NIST SP 853 as the basis for security controls for national security systems (NSS), which include DoD systems. We will also discuss how security controls are tailored for NSS, looking at CNS SI 12:53, like we did for SP 853 in part two. The alignment of DoD systems was driven by a cross-governmental working group, the JTF. Here are examples of alignments and changes fostered by this group. Note that some of the items on the left side, like "daya cap," remain well-known terms that have existed on the Internet for a long time. Key reference documents we will discuss are Department of Defense Instruction 8,500.01, whose subject is cybersecurity, and DoD 85,100.1, the RMF for DoD IT. We covered NIST SP 853 in part two, so we'll only touch on it here. It is a fundamental reference to the more visible SI NSA 1253. The website has links for all of these terms, from information assurance to cybersecurity. It was called out in DoD I 8500.l1, which is largely a policy document. Merely by reference, it incorporates a number of standards, which are listed in its first appendix called Enclosure 1. For example, Enclosure 1 calls out these three standards, which we saw in...
Award-winning PDF software





Dod instructions Form: What You Should Know
S. Tax return –––- — — — –– — –– –– –– — Department of Homeland Security Department of Homeland Security Instruction 7240.3, employment Related Training Programs'' is updated to require the employment related training courses completed by applicants who have completed the Job Training and Employment Skills Program (ITES) or other approved Department of Homeland Security (DHS) education course in the field of law enforcement. DHS Instruction 7240.9, recognition and Support for Domestic Cooperation Programs'' is updated to clarify requirements for the recognition, and assistance in identifying, any alien who has successfully completed a DHS domestic cooperation certification training program provided outside the U.S. If a prior-year alien has successfully completed a DHS domestic cooperation training program in the U.S. in the prior calendar year, such alien shall be classified in the same manner as any other person receiving such training in the U.S. The Department of Homeland Security (DHS) Directive 7240.7 is removed. DHS Instruction 7240.9 is amended to clarify that for purposes of this change, the term ‹employee› means a DHS worker or civilian employee in the service or functions of the DHS. DHS Instruction 7240.8 is amended to clarify the requirements for the receipt of, and award to, an alien for employment under the ITES. Department of the Treasury | Financial Crimes Enforcement Network (Fin CEN) (Updated 2/18/2018). Directive 469, ‹Fin CEN Procedures for the Certification of a Foreign Corporation to Operate in the United States, is amended. The Directive does not supersede any other Fin CEN regulation. The Directive does create a new entity, the Domestic Export Security Operations Center (DESOC), to serve as the central point for coordination of federal government requirements with respect to the qualification of foreign jurisdictions and persons for export and reexport licenses under Section 942 of the USA PATRIOT Act and U.S. regulations. The Directive does not provide new authority for the U.S. Secretary of the Treasury or the Administrator of the United States Agency for International Development (USAID) to grant such licenses. The Directive does require domestic entities for the international export and reexport of U.S. commodities or services, who do not possess a license with regard to the category of the transaction, to apply for a license.
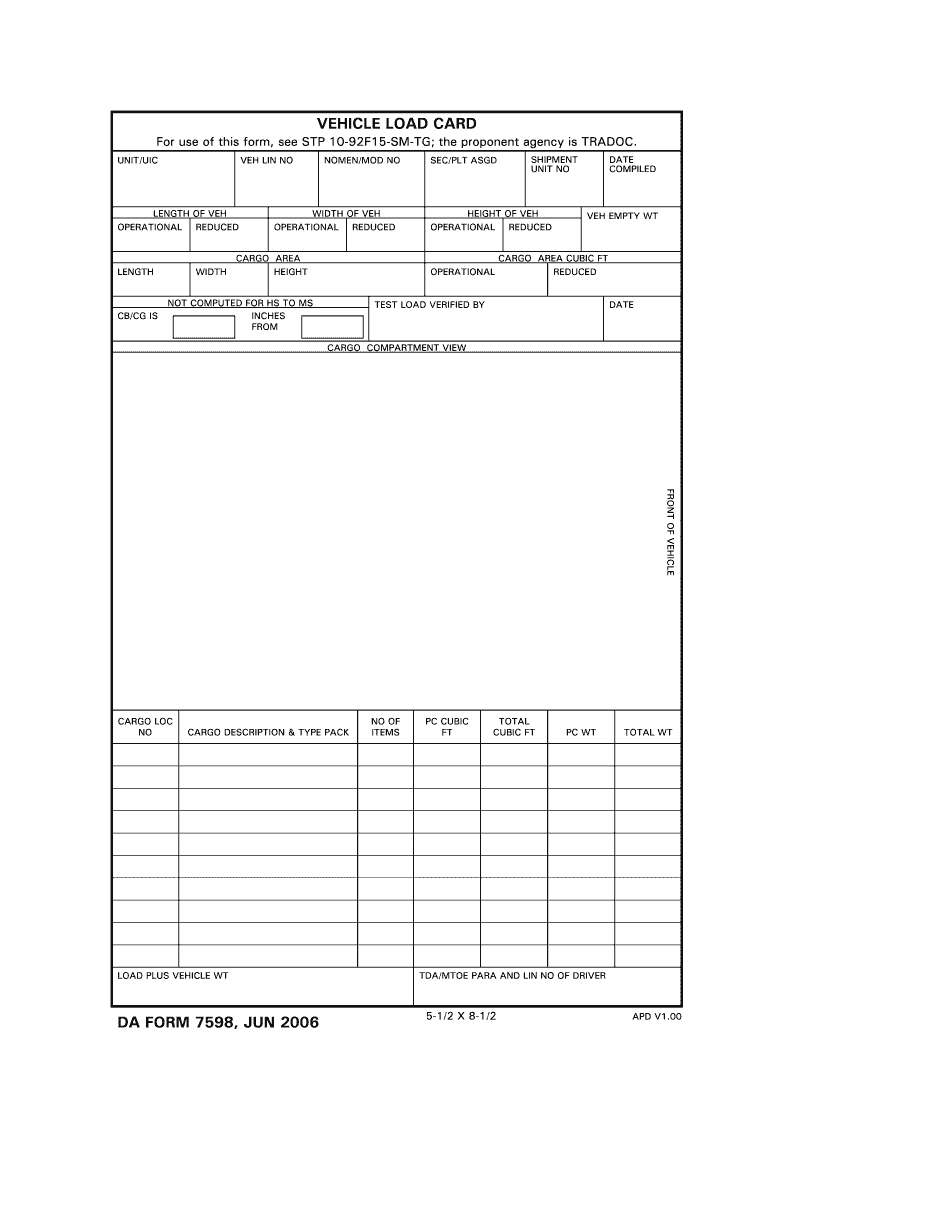
online solutions help you to manage your record administration along with raise the efficiency of the workflows. Stick to the fast guide to do Da Form 7598, steer clear of blunders along with furnish it in a timely manner:
How to complete any Da Form 7598 online: - On the site with all the document, click on Begin immediately along with complete for the editor.
- Use your indications to submit established track record areas.
- Add your own info and speak to data.
- Make sure that you enter correct details and numbers throughout suitable areas.
- Very carefully confirm the content of the form as well as grammar along with punctuational.
- Navigate to Support area when you have questions or perhaps handle our assistance team.
- Place an electronic digital unique in your Da Form 7598 by using Sign Device.
- After the form is fully gone, media Completed.
- Deliver the particular prepared document by way of electronic mail or facsimile, art print it out or perhaps reduce the gadget.
PDF editor permits you to help make changes to your Da Form 7598 from the internet connected gadget, personalize it based on your requirements, indicator this in electronic format and also disperse differently.
Video instructions and help with filling out and completing Dod instructions